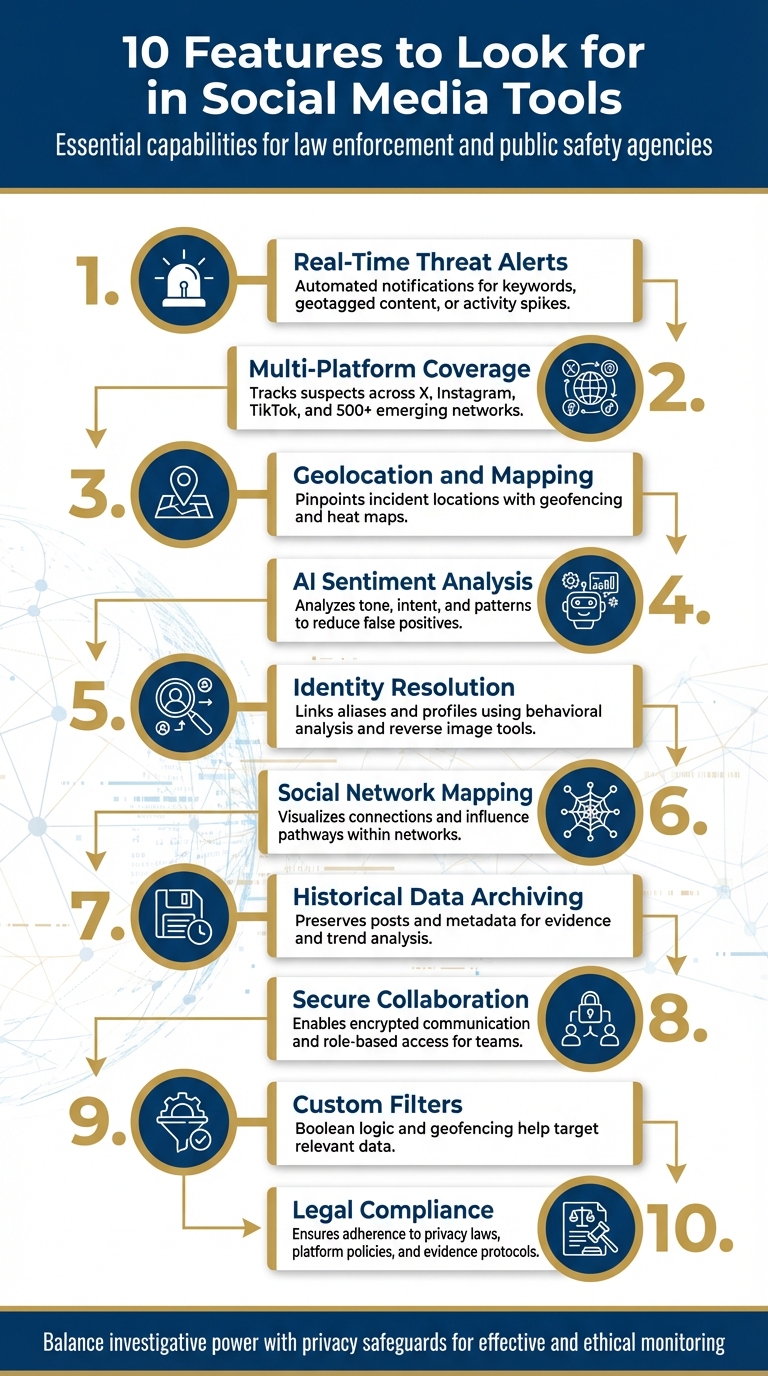
10 Features to Look for in Social Media Tools
Social media tools are essential for law enforcement and public safety agencies to monitor threats, gather intelligence, and ensure compliance with privacy laws. With billions of posts generated daily, manual tracking is no longer effective. The right tools can automate monitoring, analyze data, and provide actionable insights. Here are 10 key features to look for:
- Real-Time Threat Alerts: Automated notifications for keywords, geotagged content, or activity spikes.
- Multi-Platform Coverage: Tracks suspects across platforms like X, Instagram, TikTok, and emerging networks.
- Geolocation and Mapping: Pinpoints incident locations with geofencing and heat maps.
- AI Sentiment Analysis: Analyzes tone, intent, and patterns to reduce false positives.
- Identity Resolution: Links aliases and profiles using behavioral analysis and reverse image tools.
- Social Network Mapping: Visualizes connections and influence pathways within networks.
- Historical Data Archiving: Preserves posts and metadata for evidence and trend analysis.
- Secure Collaboration: Enables encrypted communication and role-based access for teams.
- Custom Filters: Boolean logic and geofencing help target relevant data.
- Legal Compliance: Ensures adherence to privacy laws, platform policies, and evidence protocols.
These features help agencies respond to threats quickly while maintaining legal and ethical standards. The right tool balances investigative power with privacy safeguards.
10 Essential Features for Law Enforcement Social Media Monitoring Tools
1. Real-Time Threat Detection and Alerts
Automated real-time alerts play a crucial role in maintaining safety. Today’s social media monitoring tools can scan through millions of posts in just minutes, providing instant notifications when certain keywords spike, message volumes exceed normal levels, or geotagged content emerges from high-risk locations.
This technology has become essential for gaining early situational awareness during active threats. For example, platforms like Dataminr First Alert provide eyewitness accounts, live images, and videos well before traditional media outlets report on incidents. This allows emergency services to act quickly and efficiently.
These systems go beyond basic monitoring by incorporating advanced geolocation and filtering techniques to identify critical threats more precisely. Tools equipped with geofencing and heat mapping can pinpoint exact incident locations, enabling dispatchers to send response teams without delay. Additionally, features like Boolean logic and advanced filtering help minimize false positives, distinguishing real threats from jokes or harmless memes that could otherwise lead to unnecessary responses. For instance, the Florida Department of Law Enforcement invested $195,844 in monitoring software to ensure they could gather actionable intelligence effectively.
Alerts can be configured to reach field officers instantly through text, voice, email, or app notifications. Automated notifications can also be set up to detect activity bursts that might indicate planned violence, gang-related actions, or civil unrest.
sbb-itb-a73accb
2. Multi-Platform Coverage Across Social Networks
After receiving threat alerts, monitoring activity across multiple social networks becomes critical for keeping tabs on suspects who move between platforms to avoid detection.
Threat actors often jump from popular platforms like X and Instagram to newer options like Bluesky and Mastodon, as well as smaller, niche forums. Keeping an eye on all these spaces ensures investigators don’t lose track when suspects switch platforms, maintaining a clear digital trail.
Each network offers distinct insights. For example, X is ideal for real-time updates during live events, while Instagram and TikTok provide valuable geotagged content that helps track movements and locations. Decentralized platforms like Bluesky and Mastodon can host coordinated activities that are harder to moderate compared to mainstream networks.
By monitoring multiple platforms, investigators can piece together fragmented digital clues to uncover aliases and build a complete picture of a suspect's activity. With advanced OSINT tools, data from over 500 platforms can be analyzed, connecting timestamps and locations to reveal criminal networks. This approach helps overcome platform-specific challenges, especially since over 70% of U.S. adults use social media and many suspects manage accounts across different networks.
"Full-spectrum security coverage eliminates blind spots when threat actors move between different platforms." - ShadowDragon
However, the sheer volume of data - billions of posts every day - combined with API restrictions from major platforms, presents a significant challenge. To address this, agencies need tools that can gather and consolidate data from both mainstream platforms and smaller, specialized forums, ensuring no intelligence is lost in silos.
3. Geolocation and Mapping Capabilities
Once threats are identified, geolocation bridges the gap between digital data and real-world action by pinpointing their physical origins. This allows for a quick and coordinated response. Social media data, when combined with location-based tracking, can be transformed into exact physical coordinates.
Geofencing plays a critical role here. It creates virtual boundaries around specific areas - such as disaster zones, borders, or high-risk neighborhoods - enabling agencies to monitor and collect social media data exclusively from within those zones. This method filters out irrelevant, nonlocal data and narrows the focus to a designated jurisdiction. For example, during Hurricane Sandy in October 2012, FEMA relied on geolocated media posts and distress signal tags from social media to prioritize search and rescue operations. This kind of precise data can also be used to develop visual tools like heat maps, which help anticipate potential threats.
Heat maps are particularly useful for visualizing areas where digital activity is surging. A sudden increase in posts can indicate the epicenter of a developing disturbance or threat. French authorities used this technique during the Yellow Vest protests, which began in late 2018, to track planned protest routes and identify gathering spots, ultimately improving crowd safety measures.
"Geofenced monitoring limits data collection to specific locations. Real-time monitoring becomes vital when tracking social disturbances and border surveillance activities." - ShadowDragon
Location data can be extracted from various sources, such as explicit check-ins, image metadata (EXIF), tagged locations, and even indirect geographic cues. For instance, during the Freddie Gray protests, the Baltimore Police Department utilized geolocated social media images and facial recognition to identify individuals with outstanding warrants. By combining location data from consumer reports, social media posts, and metadata, agencies can create powerful visualizations that merge physical and digital information.
4. AI-Powered Sentiment and Pattern Analysis
AI-powered sentiment and pattern analysis takes real-time threat detection a step further by offering a deeper understanding of online conversations and behaviors.
This technology goes beyond simple keyword detection by analyzing the context, intent, and emotional intensity behind language. For example, it avoids misinterpreting phrases like "bomb pizza" as a threat, which might happen with keyword-only alerts. Instead, it focuses on the meaning and tone of the content, reducing false positives.
AI also helps distinguish between genuine public concern and coordinated manipulation. It identifies individuals or groups with unusually high engagement, allowing for prioritized review. Platforms like Babel Street can analyze sentiment in over 50 languages, ensuring agencies can monitor diverse communities without being hindered by language barriers.
"Sentiment analysis measures tone, intent, and volatility to discern whether viral content stems from support mechanisms or manipulative tactics aimed at triggering public outrage." - ShadowDragon
AI tools also detect unusual patterns, such as sudden spikes in followers, rapid changes in posting frequency, or shifts in language use - indicators of coordinated activity. By tracking how narratives evolve and measuring emotional escalation over time, these tools offer predictive insights. This allows agencies to move from reacting to threats to preventing them before they materialize.
However, AI isn’t flawless. A 2017 study revealed that some tools misinterpreted African American Vernacular English (AAVE), highlighting the importance of human oversight to validate AI findings. When combined with cross-source verification, AI-powered sentiment analysis becomes a powerful tool, cutting through the noise and helping focus resources on real threats. This detailed approach works alongside broader monitoring strategies to support proactive decision-making.
5. Identity Resolution and Alias Unmasking
AI-driven sentiment analysis opens the door to identity resolution, a process that connects scattered digital traces to confirm suspect identities.
When individuals use multiple usernames or fake profiles, identity resolution tools step in to link these fragmented traces. By connecting aliases to a single person, investigators can generate actionable intelligence. Tools like pivot analysis make this process more efficient. Starting with just one data point - like an email address, phone number, or username - these tools scour hundreds of platforms to find linked accounts, even when usernames vary slightly, such as "j0hn_d03" versus "johndoe2024". For instance, ShadowDragon Horizon taps into over 500 online platforms to uncover these connections, laying the groundwork for deeper investigations.
Visual identification plays a crucial role here. Reverse image search engines and facial recognition tools, such as PimEyes, scan the internet to track where the same profile picture or facial features appear under different names. Beyond visuals, behavioral analysis digs into patterns like posting schedules, writing styles, and even emoji usage to identify whether multiple accounts share the same digital habits.
Social network mapping takes it a step further by revealing hidden relationships. By analyzing friend lists, mentions, and interactions, investigators can spot patterns. For example, if two seemingly unrelated accounts frequently engage with the same small group of users, it could suggest they belong to the same person. Media Sonar excels at this, compiling digital snapshots by correlating data from over 300 sources and billions of public records.
Even with these advanced tools, human verification remains critical. Automated systems can misinterpret slang or generate false positives, so analysts must corroborate AI findings with additional evidence. Investigators are also encouraged to use non-attributable browsing methods to avoid tipping off suspects through features like "suggested friends" notifications. These precautions ensure the integrity of the investigation while minimizing risks.
6. Social Network Mapping and Relationship Analysis
After identifying aliases and understanding behavioral patterns, the next step is to map connections. This process uncovers hidden networks and influence pathways, offering deeper insights into group dynamics. Social network mapping tools transform raw data into interactive visuals, making it easier to spot clusters, unseen links, and patterns of influence within criminal or suspicious networks.
These tools highlight both direct and indirect connections, flagging potential hidden links when accounts frequently interact with the same groups. For example, the Chicago Police Department has used this method to monitor gang communications and online turf disputes. By leveraging network maps, they’ve been able to predict retaliatory shootings and intervene before violence escalates in the physical world. These visualizations also pave the way for analyzing the intensity of interactions within these networks.
Advanced tools go a step further by quantifying the strength of connections. They analyze how often individuals interact and the nature of those interactions, helping investigators identify key players who are deeply invested - whether emotionally or ideologically. A notable application of this approach occurred during the 2020 U.S. election, when CISA used network mapping to track coordinated disinformation campaigns, demonstrating how these tools can pinpoint influential sources. This level of detail ensures investigators can choose the right tools to maintain evidence integrity.
For effective results, it’s crucial to use platforms that integrate data from diverse sources. This means pulling information from mainstream social networks, encrypted messaging apps, and niche forums. Automated link analysis is also essential - it can process millions of data points in minutes, far outpacing what manual searches can achieve. Lastly, if the relationship maps are intended for legal proceedings, ensure the tool supports chain-of-custody protocols and includes timestamped logs to uphold evidentiary standards.
7. Historical Data Archiving and Trend Monitoring
Once key relationships and players are identified, preserving historical data becomes crucial for effective predictive analysis. Social media content is often fleeting - posts get deleted, accounts disappear, and vital evidence can vanish in an instant. Using automated archiving tools ensures that accounts, conversations, and media are securely stored, so no critical signals are lost over time.
Archiving historical data serves two purposes: preserving evidence and uncovering long-term behavioral patterns. These patterns can play a critical role in establishing probable cause for warrants or strengthening cases for prosecution. For instance, before the London Olympics, the UK Metropolitan Police analyzed archived social media posts and metadata patterns to detect potential threats. By examining user language and posting habits, they were able to identify and intercept possible radical activities before they escalated.
"Agencies that model past trends, public sentiment changes, and behavioral patterns can predict potential unrest, policy backlash, and coordinated influence operations to take action before these threats reach critical thresholds." – ShadowDragon
The real power of historical data archiving lies in its ability to shift agencies from reactive to predictive strategies. By monitoring how public sentiment evolves, agencies can detect anomalies - like sudden spikes in specific language, rapid follower growth, or tone changes - that often signal coordinated actions or potential threats. A 2015 survey by the International Association of Police Chiefs revealed that 96.4% of law enforcement agencies used social media in some capacity, with over 75% employing it specifically for intelligence gathering.
When choosing archiving tools, it's important to prioritize those that maintain chain-of-custody protocols and provide timestamped data logs, ensuring that evidence remains admissible in court. Additionally, tools should be capable of pulling data from multiple sources - mainstream platforms, encrypted apps, and niche forums alike - to create comprehensive timelines. These timelines can help verify alibis, identify witnesses, and strengthen investigations.
8. Secure Collaboration and Case Management
When multiple investigators are working on the same case, secure collaboration tools become essential for protecting evidence and maintaining operational security. Modern case management systems should include 256-bit end-to-end encryption for all communications and file exchanges, ensuring sensitive information remains safe both during transfer and while stored. This is especially critical, as 27% of law firms reported experiencing security breaches in 2023.
Role-based access controls are another key feature, enabling administrators to define who can view, edit, or download specific files within a case. This approach ensures that only authorized personnel have access to sensitive information, while still allowing teams across departments or agencies to collaborate effectively. For instance, a lead detective might have full editing privileges on a case file, while a patrol officer assisting with interviews might only have view-only access to certain sections. Every action - whether it’s accessing, editing, or sharing a document - should be recorded in immutable audit trails, providing a clear and unalterable log for security reviews and accountability.
"A cloud-based solution can actually prove more secure, reliable, and accessible for police departments than an on-premise solution." - Michael Cunningham, Detective First Grade (Ret.), New York City Police Department
Cloud-based platforms provide additional flexibility by allowing IT administrators to centrally manage user accounts and remotely wipe data from compromised devices or those belonging to departing staff. Incorporating multifactor authentication (MFA) - preferably through authenticator apps rather than less secure SMS methods - further strengthens the security of these tools.
When choosing collaboration platforms, look for solutions that meet CJIS compliance standards and are hosted in environments tailored for law enforcement needs. Integration with existing Records Management Systems is crucial to avoid information silos, and mobile-friendly forms can help capture structured data that’s ready for courtroom use. Additionally, consider tools with customizable keyword and location filters to streamline digital investigations.
9. Customizable Keyword and Location Filters
For law enforcement agencies, sifting through endless social media chatter without proper filters can mean missing crucial information. To tackle this, customizable filters take data collection to the next level by focusing on the most relevant details. Using Boolean logic (AND, OR, NOT operators), regex for complex patterns, and entity recognition, these filters help sort through millions of posts to uncover key indicators of criminal activity. This approach builds on earlier tools like real-time threat detection and geolocation, making data collection sharper and more targeted.
Geofencing plays a big role in this precision. By narrowing data collection to specific areas - like a city block during an event or an entire county during a disaster - agencies can link digital activity to real-world events in real time. This allows them to track distress signals or monitor civil disturbances visually through heat maps and geolocated media.
Adding layers like keyword, language, time, and sentiment filters gives agencies even deeper insights. These tools can reveal intent and help prioritize high-risk content over irrelevant posts. Automated alerts, which flag sudden spikes in keyword activity, often act as early warnings for emerging crises. By combining these filters, agencies ensure they’re left with only the most actionable intelligence for deeper analysis.
"Publicly available social media content may be monitored or viewed in advance of significant public events solely to determine the resources necessary to keep participants and the public safe." – Brennan Center
To stay effective, agencies should refresh their keyword lists every 45 days. This keeps them up to date with evolving slang and coded language. Documenting these terms, along with their public safety purposes, is also crucial for staying legally compliant and accountable. On top of that, tools that cut manual reporting time by up to 80% free up analysts to focus on verifying information and responding to threats. These advanced filtering tools work hand in hand with secure collaboration and case management features, streamlining workflows for investigative teams.
10. Compliance with Legal and Privacy Standards
When law enforcement collects social media data, it must operate within strict legal frameworks to ensure constitutional rights are respected. Tools used in these operations must honor the First Amendment, which protects free speech and association, as well as the Fourth Amendment, which guards against unreasonable searches. The U.S. Supreme Court has highlighted that the Constitution was designed "to place obstacles in the way of a too permeating police surveillance." This means monitoring cannot be based on arbitrary factors like political or religious beliefs; it must be supported by clear, specific facts that tie the activity to a criminal investigation.
Adding to this complexity, social media platforms like Meta (Facebook/Instagram) and X (formerly Twitter) explicitly prohibit the use of their data for surveillance purposes. Beyond platform policies, compliance with laws like the California Consumer Privacy Act (CCPA) is essential. For federal applications, tools should ideally have FedRAMP certification, ensuring they meet high standards for secure and mission-critical operations.
Evidence Integrity and Legal Demands
To ensure evidence is admissible in court, tools must include strong chain-of-custody protocols. This involves features like timestamped data logs, detailed audit trails that record who accessed specific data and when, and mechanisms to authenticate digital evidence. According to the Brennan Center, "public social media posts that express specific and credible threats, when brought to the FBI's attention, can by themselves be all the evidence necessary to justify opening a preliminary or full investigation".
"Unchecked social media data collection has been used to threaten people's opportunities, undermine their privacy, or pervasively track their activity - often without their knowledge or consent." – White House Office of Science and Technology Policy
Privacy, Oversight, and Responsible Use
Privacy obligations go hand-in-hand with evidence protocols. Agencies should implement clear, written policies that outline their social media data practices, restrictions, and oversight mechanisms. However, only 49% of major U.S. law enforcement agencies currently have publicly available policies on this topic. Tools must also enforce strict data retention limits, ensuring information is deleted when no criminal activity is detected.
Finally, while AI-powered tools can assist in analyzing social media content, investigators should not rely on them exclusively. Automated systems can misinterpret context, such as sarcasm, slang, or song lyrics. There have even been cases where natural language processing tools misclassified African American Vernacular English as Danish with 99.9% confidence. To avoid such errors, all automated findings should undergo manual review, ensuring accurate and fair assessments.
Comparison Table of Platform Coverage
When it comes to social media monitoring, knowing which platforms a tool can access is crucial for law enforcement agencies. Different tools offer varying levels of access, often influenced by platform policies and restrictions. Below is a detailed comparison of platform support among several tools commonly used by law enforcement.
| Tool | Supported Platforms | Coverage Claims & Limitations |
|---|---|---|
| ShadowDragon Horizon | X, Facebook, Instagram, Reddit, 500+ others | Promises broad OSINT capabilities across social media, forums, and the dark web. |
| Dataminr First Alert | X (Partner), TikTok, Snapchat, Facebook, Reddit | Uses AI for real-time event detection and monitoring. |
| Media Sonar | X, Reddit, 4chan, 8chan, Telegram, TOR, i2p | Lost Facebook data access in 2017; monitors over 100,000 sources. |
| Voyager Labs | Facebook, X, Instagram, VK, TikTok, Telegram | Leverages AI to reconstruct public data from closed profiles and groups. |
| Digital Stakeout | X, Reddit, Tumblr, Disqus, WordPress | Advertises access to over 550 social networking sites. |
| Skopenow | "All major platforms", Parler | Extracts data anonymously, also includes court and consumer records. |
| Snaptrends | Facebook, X, Instagram, YouTube, Flickr, Google+ | Focuses on location-based monitoring and sentiment analysis. |
| EDGE NPD (ABTShield) | Facebook, X, Parler, Telegram | Specializes in tracking disinformation, bots, and trolls. |
Platform-Specific Strengths and Gaps
Each platform offers distinct advantages for investigations. For instance, X (formerly Twitter) is unmatched for tracking breaking news and real-time events, making it a top choice for time-sensitive cases. Platforms like Facebook and Instagram, on the other hand, excel in providing geotagged images and videos, which are invaluable for mapping suspect movements and spotting crime hotspots. Facebook’s massive user base - reaching 75% of the global population - also makes it a key resource for uncovering social connections and networks.
However, accessing data from Meta-owned platforms like Facebook and Instagram comes with legal hurdles. Some tools may rely on methods that breach platform terms of service, potentially exposing law enforcement to compliance risks.
Emerging Platform Considerations
While established platforms dominate the landscape, newer networks like Bluesky and Mastodon are beginning to gain momentum. Advanced tools claiming access to "500+ sources" often include these emerging platforms, but support can vary significantly. Mastodon, for example, operates through independent servers, making comprehensive monitoring a more complex task. Agencies should carefully evaluate each tool's ability to cover these decentralized networks to ensure both effectiveness and legal compliance. A clear understanding of platform coverage is essential for making informed decisions and staying within regulatory boundaries.
Conclusion
Selecting the right tool means finding a balance between investigative capabilities and legal accountability. The features discussed in this guide combine to create a system that prioritizes public safety while respecting individual rights. For example, real-time threat detection can be a game-changer during emergencies like active shooter events or natural disasters, while compliance safeguards ensure that agencies operate within legal and ethical boundaries.
"The best tools balance powerful investigative capabilities with strict adherence to privacy laws and ethical guidelines, ensuring that agencies can leverage social media intelligence while respecting civil liberties." - ShadowDragon
Unfortunately, many agencies still lack the tools and policies needed for responsible operations. Features like efficient reporting and legal safeguards allow investigators to concentrate on their work without overstepping boundaries. This approach not only speeds up investigations but also reinforces the importance of adhering to legal standards.
Multi-platform coverage is another crucial aspect, helping to eliminate blind spots where potential threats might hide. Meanwhile, AI-powered analytics comb through massive amounts of social media activity to identify genuine risks. That said, technology alone isn’t enough. As the White House Office of Science and Technology Policy cautions:
"Unchecked social media data collection has been used to threaten people's opportunities, undermine their privacy, or pervasively track their activity - often without their knowledge or consent"
The integration of features like real-time alerts, comprehensive archiving, audit trails, and access controls creates a secure framework that supports both public safety and legal integrity. These elements are just as important as the monitoring tools themselves, ensuring that agencies can respond quickly to threats while remaining accountable.
When choosing a tool, look for clear documentation, strict compliance with platform policies, and strong safeguards. The right solution will empower your team to act decisively on credible threats while maintaining the trust that is essential for effective law enforcement.
FAQs
How can I determine if a tool’s data collection is legally compliant?
To make sure a social media monitoring tool stays within legal boundaries, confirm it complies with privacy laws such as GDPR or applicable U.S. regulations. Check that it gathers data exclusively from public sources and does not access private information without permission. Take a close look at the vendor’s compliance policies, transparency reports, and how they manage data. Regular audits and strict adherence to legal guidelines are essential for safeguarding privacy and maintaining compliance.
What should I ask vendors to ensure evidence holds up in court?
When working with vendors, it's crucial to request documentation that confirms the integrity, authenticity, and chain of custody of their data. Their tools should offer a verifiable audit trail that clearly shows how the data was collected, stored, and maintained without any alterations.
Additionally, ask for details about their compliance with legal standards, such as the Federal Rules of Evidence, to ensure their processes meet courtroom requirements. Confirm that they use secure methods, like encryption, to protect the data from tampering and to maintain its integrity for potential legal proceedings.
How can teams reduce AI false positives without missing real threats?
Reducing AI false positives while pinpointing genuine threats requires a mix of technology and human oversight. Teams can leverage advanced OSINT tools that incorporate contextual analysis to better differentiate harmless activities from malicious ones. Adding layers of verification - like manual reviews or cross-checking intelligence from multiple sources - helps cut down on mistakes. Continuously fine-tuning AI algorithms using feedback and the latest threat intelligence ensures the system becomes more accurate over time, striking a balance between staying alert and avoiding unnecessary alerts.
Last updated: February 14, 2026